Private VPNs and proxy servers are an increasingly in-demand and popular IT service. There are several reasons why people are looking for them. Some want to protect their privacy and anonymity on the Internet. Others try to bypass geo-blocking and access websites with restricted access in their countries. You can either buy access to a commercial solution or configure your own proxy server on an AWS EC2 instance. If you don’t have an AWS account yet, you can use the Free Tier and have your proxy server free of charge within certain usage limits.
Setup of EC2 instance
I won’t describe the entire process of configuring your instance because I assume that you have at least a basic understanding of how AWS EC2 works. However, I will briefly explain all of the steps. In order to create an instance, go to the EC2 service and click the “Launch instance” button. Let’s go through the process step by step:
- Choose AMI – select Ubuntu Server 20.04 LTS (HVM)
- Choose Instance Type – select t2.micro (probably t2.nano would be also sufficient)
- Configure Instance – leave everything as is
- Add Storage – default 8GB (gp2 type) is ok
- Add Tags – we don’t need tags, click Next
- Configure Security Group – create a new group and add rules to allow access on TCP ports 22 (SSH) and 3128.

Ultimately, you should restrict access (especially to SSH) only for your IP addresses! The configuration above, with the source set to “Anywhere”, is only intended for testing.
7. Review – your review page should look like on the screenshot below.

If everything is correct, finish the configuration process by creating a new key pair (or choose one of the existing ones if you have any). After that, we can start the installation and configuration of the tools we need.
If you want to have a static and invariable IP address associated with your EC2 instance, you need to allocate an Elastic IP. Instructions how to allocate and associate Elastic IP address are available in the official AWS documentation.
Server-side configuration
First, log in to the server using the EC2 instance IP address and your key pair created before. For Ubuntu-based instances, the username of the default user is Ubuntu. Remember to replace an IP address with your own one!
ssh ubuntu@18.193.223.127 -i /path/to/your/key.pem
When we access the instance, we can start the configuration. We are going to use Tinyproxy as a proxy daemon. Let’s start with the update of our operating system and installation of Tinyproxy.
sudo apt-get update sudo apt-get upgrade -y sudo apt-get install tinyproxy -y
Afterward, we need to update the configuration file located at /etc/tinyproxy/tinyproxy.conf. Just find #Listen 192.168.0.1 and replace it with Listen 127.0.0.1. Then save the file. The last thing you have to do is to restart Tinyproxy in order to load the new configuration.
sudo service tinyproxy restart
From now on the proxy will accept requests only from the localhost.
Server-side encryption
By default, Tinyproxy does not provide any encryption features. In order to encrypt the communication between your computer and the proxy server, we are going to use Stunnel. Firstly, let’s install Stunnel on the server.
sudo apt-get install stunnel
I use Stunnel v5.56 (default in Ubuntu 20). Older versions may be disabled by default after installation. If so, replace ENABLED=0 with ENABLED=1 in /etc/default/stunnel4. Then restart Stunnel. If you don’t see the ENABLED parameter in that file, that means you don’t need to worry about it.
Before we go to the Stunnel configuration, we have to generate a certificate and a private key. They are required to enable encryption of the communication. The location of the keys is up to you. I like to have them in etc/stunnel/ssl/.
sudo mkdir /etc/stunnel/ssl sudo openssl genrsa -out /etc/stunnel/ssl/key.pem 4096 sudo openssl req -new -x509 -key /etc/stunnel/ssl/key.pem -out /etc/stunnel/ssl/cert.pem
You are going to be asked for some information like country code, organization name, etc. You can fill some of them or just hit enter few times and accept default values. It does not matter when you don’t represent a company.
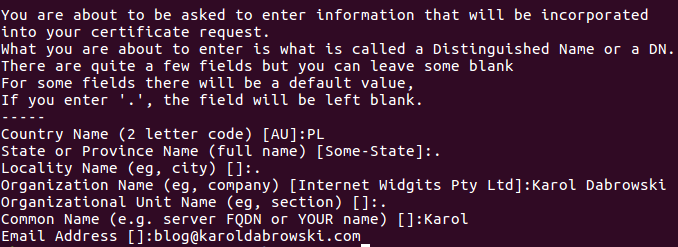
By default certificates issued with OpenSSL are valid for 30 days. If you want your certificate to be valid longer, use -days parameter.
sudo openssl req -new -x509 -key /etc/stunnel/ssl/key.pem -out /etc/stunnel/ssl/cert.pem -days 365
The certificate issued that way will be valid for 365 days.
When we have the certificate generated, we can configure Stunnel. Let’s create a config file in /etc/stunnel/ directory. The file name can be anything but must have a *.conf extension. In my case, it’s just stunnel.conf.
# /etc/stunnel/stunnel.conf client = no [proxy] accept = 0.0.0.0:3128 connect = 127.0.0.1:8888 cert = /etc/stunnel/ssl/cert.pem key = /etc/stunnel/ssl/key.pem
- client = no – tells Stunnel that this instance is used as a server, not a client. It’s a default value so you can easily skip it. However, I like to have it explicitly specified.
- [proxy] – service name, is required by Stunnel and can be anything.
- accept = 0.0.0.0:3128 – accept requests from all IP addresses.
- connect = 127.0.0.1:8888 – pass a decrypted request to port 8888 where Tinyproxy is listening on.
- cert = /etc/stunnel/ssl/cert.pem – path to the cert file.
- key = /etc/stunnel/ssl/key.pem – path to the private key file.
Afterward, you have to restart Stunnel to load the new configuration.
sudo service stunnel4 restart
And that’s all, our proxy server is set up!
Client-side configuration
When our proxy server is ready, we can focus on the configuration of a client. We will need to install Stunnel just like on the server.
sudo apt-get update sudo apt-get upgrade -y sudo apt-get install stunnel
If you don’t use up to date version of Stunnel, please read the information in the alert frame in the previous paragraph. It’s possible that you would need to enable Stunnel before you could use it.
Now you need to copy the certificate you generated in the previous step from your server. You can just open the cert file on the server (using for instance nano or cat command), copy the content and paste it to a local file. In my case, the location is the same as on the server that is /etc/stunnel/ssl/cert.pem. Alternatively, you can use scp command to copy the certificate from the server to your local machine directly.
sudo mkdir /etc/stunnel/ssl sudo scp -i /path/to/your/key.pem ubuntu@18.193.223.127:/etc/stunnel/ssl/cert.pem /etc/stunnel/ssl/cert.pem
The last thing to do in this step is Stunnel setup. In order to to that, let’s create a configuration file.
# /etc/stunnel/stunnel.conf client = yes [proxy] accept = 127.0.0.1:3128 connect = 18.193.223.127:3128 verify = 4 CAFile = /etc/stunnel/ssl/cert.pem
The configuration file looks similar as the one on the server. I will skip parameters I described in the previous step and only explain the new ones.
- verify = 4 – level of the cert verification. The official documentation describes level 4 as follows “Ignore the chain and only verify the peer certificate.“
- CAFile = /etc/stunnel/ssl/cert.pem – path to the local cert file.
At the end restart Stunnel to load your new configuration.
sudo service stunnel4 restart
Browser configuration
Finally, when we have both proxy server and client set up, we can configure a web browser to use that proxy. I use Firefox so the instruction will be focused on that browser. However, you should have no problem doing this on any other browser.
In Firefox, you can find proxy setting in Preferences > Network Settings > Settings.
In the popup window that will show up when you click the Setting button check Manual proxy configuration and enter 127.0.0.1 in the HTTP Proxy field and 3128 in the Port field. Repeat that for HTTPS Proxy and Port fields. Correct configuration is presented in the screenshot below. After all, click OK button.

That was the last step! From now on your proxy should work. You can test it for example by entering phrase “My IP” in Google or visiting any website showing the visitor’s IP address.

Summary
Thanks to open-source tools like Tinyproxy and Stunnel, creating a proxy server is very simple. It should take less than half an hour for someone with a basic understanding of EC2 service. Moreover, you can take advantage of the cloud features and turn on your EC2 instance (and pay for it) only when you need it! For this reason, the cost of your proxy can be really low!